While Commander can authenticate with AWS using static keys, best practice dictates authentication through an IAM role for any application that’s deployed in AWS and will access AWS resources.
An instance profile is a container for an IAM role that you can use to pass role information to an EC2 instance when the instance starts. The CloudFormation template includes a parameter for you to specify an instance profile, so that the desired role is applied to the EC2 instance hosting Commander.
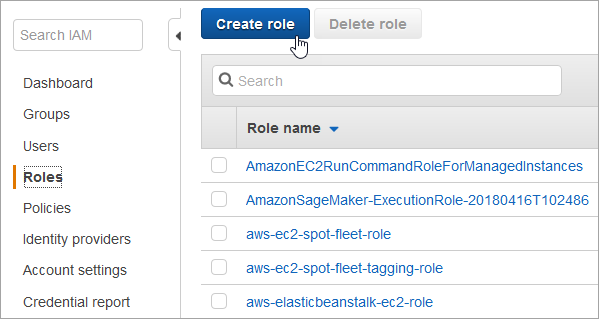
- Sign in to AWS IAM Role Management as an administrator of the account where Commander will be deployed.
- Click Create role.
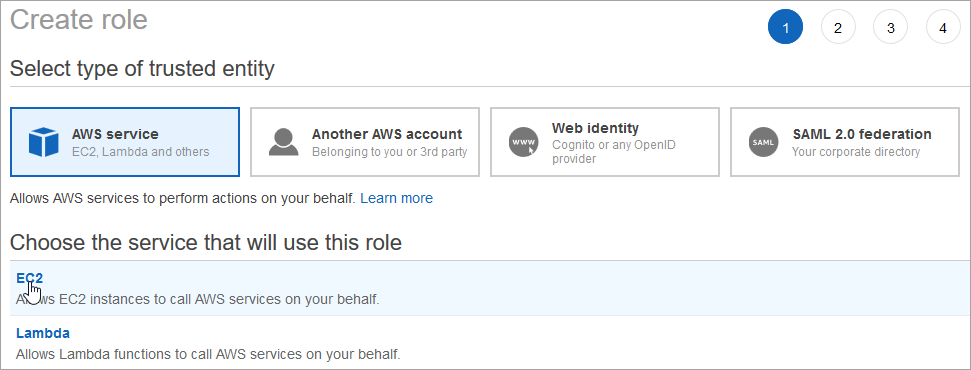
- On the Create role page, make sure AWS service is selected, click EC2, and click Next: Permissions.
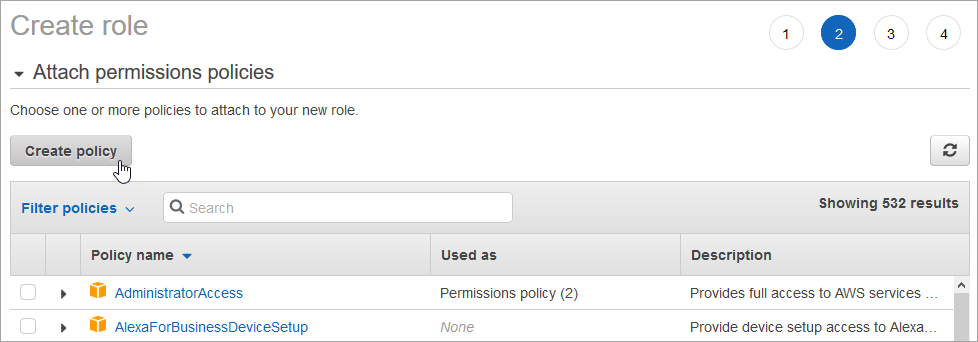
- On the Create role page, click Create policy.
A new browser window or tab appears, displaying the Create policy page.
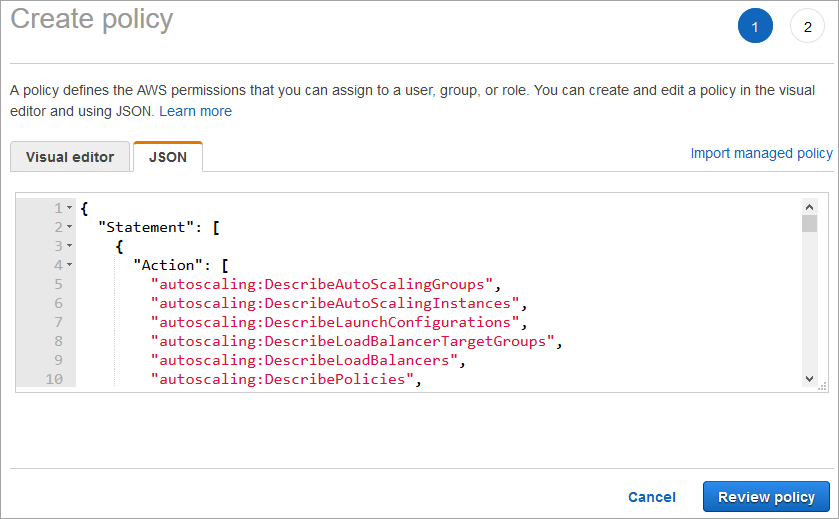
- Click the JSON tab.
- Paste the IAM Policy from AWS Configuration Files into the text box.
Some customization of this policy may be required depending on the level of service of that Commander will provide.
This policy grants Commander administrative permission to manage specific resources in the account. Note that while you may customize this policy, Commander must have administrative permissions in order to manage resources in the account.
- Click Review policy.
- On the Review policy page, enter a name such as "CommanderAdminPolicy" and an optional description, then click Create policy.
A message is displayed to indicate that the policy was created.
- Return to the browser window or tab displaying the Create role page.
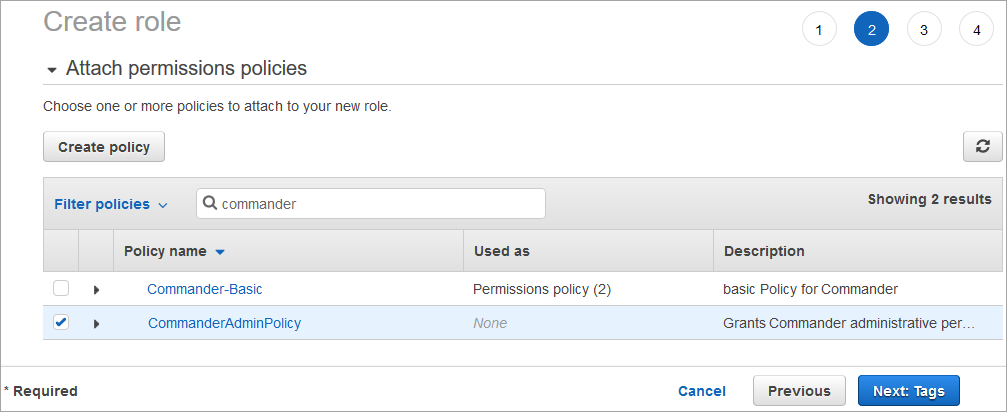
- In the Filter policies search box, enter text to locate the policy you created.
You may have to refresh your view to see the new policy.
- Select your new policy.
- Click Next: Tags.
- If desired, add tags to the role and click Next: Review.
- On the Review page, enter a name such as "CmdrInstanceProfileRole".
- Click Create role.
A message appears, indicating that the role was created.
The CloudFormation template includes a parameter for you to specify this instance profile, so that the role is applied to the EC2 instance hosting Commander.
Snow Software does not own the third party trademarks, software, products, or tools (collectively, the “Third Party Products”) referenced herein. Third Party Product updates, including user interface updates, may not be reflected in this content.